- Main
- Computers - Operating Systems
- Practical Linux Forensics: A Guide for...

Practical Linux Forensics: A Guide for Digital Investigators (Final Release)
Bruce Nikkel你有多喜欢这本书?
下载文件的质量如何?
下载该书,以评价其质量
下载文件的质量如何?
Practical Linux Forensics dives into the technical details of analyzing postmortem forensic images of Linux systems that have been misused, abused, or the target of malicious attacks. This essential practitioner’s guide will show you how to locate and interpret digital evidence found on Linux desktops, servers, and IoT devices, draw logical conclusions, and reconstruct timelines of past activity after a crime or security incident. It's a book written for investigators with varying levels of Linux experience, and the techniques shown are independent of the forensic analysis platform and tools used.
Early chapters provide an overview of digital forensics as well as an introduction to the Linux operating system and popular distributions. From there, the book describes the analysis of storage, filesystems, files and directories, installed software packages, and logs. Special focus is given to examining human user activity such as logins, desktop environments and artifacts, home directories, regional settings, and peripheral devices used.
You’ll learn how to:
• Analyze partition tables, volume management, Linux filesystems, and directory layout
• Reconstruct the Linux startup process, from system boot and kernel initialization, to systemd unit files leading up to a graphical login
• Perform historical analysis of power, temperature, and physical environment, and find evidence of sleep, hibernation, shutdowns, reboots, and crashes
• Analyze network configuration, including interfaces, addresses, network managers, DNS, wireless artifacts, VPNs, firewalls, and proxy settings
• Perform analysis of time and locale settings, internationalization (language and keyboard settings), and Linux geolocation services
• Reconstruct user login sessions, analyze desktop artifacts, and identify traces of attached peripheral devices, including disks, printers, and mobile devices
Early chapters provide an overview of digital forensics as well as an introduction to the Linux operating system and popular distributions. From there, the book describes the analysis of storage, filesystems, files and directories, installed software packages, and logs. Special focus is given to examining human user activity such as logins, desktop environments and artifacts, home directories, regional settings, and peripheral devices used.
You’ll learn how to:
• Analyze partition tables, volume management, Linux filesystems, and directory layout
• Reconstruct the Linux startup process, from system boot and kernel initialization, to systemd unit files leading up to a graphical login
• Perform historical analysis of power, temperature, and physical environment, and find evidence of sleep, hibernation, shutdowns, reboots, and crashes
• Analyze network configuration, including interfaces, addresses, network managers, DNS, wireless artifacts, VPNs, firewalls, and proxy settings
• Perform analysis of time and locale settings, internationalization (language and keyboard settings), and Linux geolocation services
• Reconstruct user login sessions, analyze desktop artifacts, and identify traces of attached peripheral devices, including disks, printers, and mobile devices
年:
2021
出版:
1
出版社:
No Starch Press
语言:
english
页:
400
ISBN 10:
171850196X
ISBN 13:
9781718501966
文件:
PDF, 4.99 MB
您的标签:
IPFS:
CID , CID Blake2b
english, 2021
在1-5分钟内,文件将被发送到您的电子邮件。
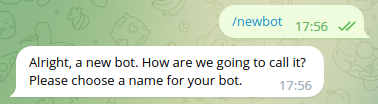
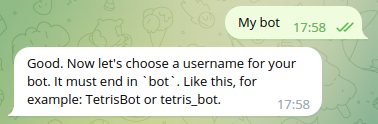
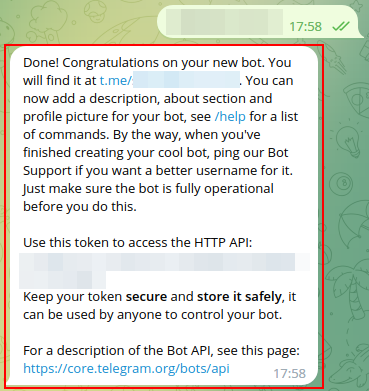
该文件将通过电报信使发送给您。 您最多可能需要 1-5 分钟才能收到它。
注意:确保您已将您的帐户链接到 Z-Library Telegram 机器人。
该文件将发送到您的 Kindle 帐户。 您最多可能需要 1-5 分钟才能收到它。
请注意:您需要验证要发送到Kindle的每本书。检查您的邮箱中是否有来自亚马逊Kindle的验证电子邮件。
正在转换
转换为 失败
关键词
关联书单

























































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  转换文件
转换文件 更多搜索结果
更多搜索结果 其他特权
其他特权